What is a tunnel in networking?
You may have heard about a device called VPN Concentrator in connection with setting up a Virtual Private Network (VPN) which allows safe access to your home or business network remotely by the users of your network while they are away.
The Concentrator VPN creates a virtual private network by establishing a secure connection called a tunnel. Many of us may not know what is a tunnel in networking.
Before I go to explain what is a VPN Concentrator and what does it do, I am going to give an overview of the use of VPN Technology to ensure the fastest and safest possible connection to the internet through a VPN service.
Let’s first see what is a VPN and how does VPN works.
What is a VPN?
A VPN protocol is the technology that provides one of the most reliable and resilient advanced network services. It is a service that enables users to access the internet safely and privately by routing their connections through a server that helps to shield their identity and location to remain anonymous on the net. Thus VPN enables users to send and receive data across shared or public networks as if their computing devices are directly connected to a safe private network.
How does a VPN work?
VPN creates a safe and encrypted connection over a less secure network, between the device and the network so that the users who need to access their home or business network can simply log into their VPN from anywhere in the world and use the network as if they are physically present in their home or office.
A VPN establishes a virtual point-to-point connection through the use of tunneling protocols over the existing networks to encrypt data at the sending end and decrypt it at the receiving end. Thus through VPN service all sensitive data can be safely accessed or transmitted remotely and no unauthorized person, including the hackers, can see your activities. Because of this increased security VPN service is widely used in a business/corporate environment. Two leading types of Secure VPN technology are IPsec and SSL. IPsec stands for Internet Protocol (IP) security, and it refers to a suite of protocols that secure data traveling over IP networks. Unlike a regular internet connection that doesn’t use IPsec, most VPN concentrators rely on IPsec encryption to protect your information as it moves through the VPN tunnel. This provides end-to-end encryption, effectively scrambling data at the transmitting device and unscrambling it only at the receiving end, ensuring your sensitive information remains confidential throughout its journey.
To set up a VPN, you can either go for a VPN Concentrator or go for a VPN Router having VPN functionality included in it.
What is a tunnel in networking?
Tunneling is a protocol for transferring data securely from one network to another. Network tunnels provide a direct connection between a remote server and the local network, and the transmission of data is undetectable by the public network. Network tunneling works by wrapping data in encapsulated packets that look like normal traffic on the public network.
What is a VPN Concentrator?
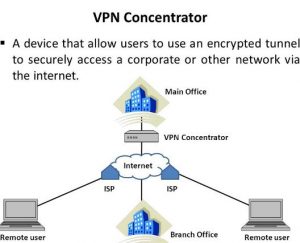
Now what is VPN Concentrator? A Concentrator VPN is a networking device that allows people to access a network remotely from anywhere in the world through multiple encrypted VPN tunnels between the user’s device and the network. It provides a secure and encrypted connection between different VPN nodes. VPN concentrators are used by large businesses that operate multiple systems that are connected using a network.
Difference Between a VPN and a VPN Concentrator
It’s easy to get the two mixed up, but there’s a key distinction to make here. A VPN is essentially the service or protocol that lets an individual securely connect to a remote network over the internet—think of it as your personal encrypted tunnel when you want privacy online, no matter where you are.
A VPN concentrator, on the other hand, steps up the game for organizations. While a standard VPN might suit solo users or small offices, a VPN concentrator is a specialized piece of hardware (or sometimes software) designed to handle dozens, hundreds, or even thousands of simultaneous VPN connections. It efficiently manages these multiple encrypted tunnels, ensuring everything runs smoothly. This makes the VPN concentrator ideal for large companies or institutions with distributed teams, where providing secure, reliable remote access at scale is paramount. With its centralized control, the network admin can easily monitor and manage connections for an entire organization—all with robust security.
Where is a VPN Concentrator Placed in a Network?
A VPN concentrator is usually installed at a strategic point within the network architecture—specifically, it sits right behind your business firewall but before the main router. This placement ensures that all VPN traffic, whether coming from remote employees or other office branches, passes through the firewall for extra protection before being routed to its destination. By putting the concentrator here, organizations like tech firms, banks, and global enterprises can efficiently manage secure remote connections while keeping the core network shielded from outside threats.
This setup makes it easy for the VPN concentrator to handle a large number of encrypted connections without exposing the rest of the network to unnecessary risk.
What protocol is best for VPN concentrators?
When choosing a protocol for VPN concentrators, scalability and robust security are key factors. Among the available options, IPsec (Internet Protocol Security) stands out due to its ability to handle connections from numerous users across dispersed networks, making it the preferred protocol for larger organizations and enterprise environments. IPsec’s combination of authentication, encryption, and key management ensures that even when hundreds or thousands of connections are involved, data remains secure and private.
OpenVPN is another widely adopted protocol for VPN concentrators. It uses SSL/TLS for key exchange, providing flexibility and strong security and allowing it to work well in varied networking environments. Many businesses opt for OpenVPN for its open-source reliability and compatibility with most modern platforms.
In short, if you’re setting up a VPN concentrator for broad, multi-user access—in offices, financial institutions, or distributed teams—IPsec and OpenVPN are the leading choices, providing a solid blend of protection, performance, and scalability.
Supported Encryption Protocols for VPN Concentrators
VPN concentrators have to juggle a variety of encryption protocols to fit different needs—from legacy compatibility to robust security for modern workplaces. Here’s a breakdown of the main protocol types you’ll commonly encounter:
- PPTP with MPPE: The Point-to-Point Tunneling Protocol (PPTP), when paired with Microsoft Point-to-Point Encryption (MPPE), was once the go-to option for basic VPN setups. It’s quick to configure and widely supported but now largely considered outdated due to known security weaknesses. While PPTP does the tunneling, MPPE handles the encryption. Still, for any situation that demands stronger data protection, other protocols are recommended.
- L2TP/IPsec: Layer 2 Tunneling Protocol (L2TP) is often deployed alongside IPsec. L2TP handles the tunneling aspect, while IPsec provides the encryption muscle. This combo is particularly handy in environments where support for legacy systems is important, though it’s also frequently seen in newer remote-access scenarios thanks to its reliable security profile.
- IPsec: Internet Protocol Security (IPsec) is a powerhouse protocol suite that delivers both encryption and authentication. Used extensively in enterprise VPN concentrators, IPsec supports multiple modes—transport and tunnel—giving organizations flexibility in how they secure and route traffic. Its high level of security makes it the standard for large-scale deployments.
- SSL/TLS: Secure Sockets Layer (SSL) and its modern successor, Transport Layer Security (TLS), offer another popular avenue for encrypting VPN connections, especially when browser-based access is required. These protocols let users securely connect without needing specialized VPN software, making them ideal in settings with diverse device types or bring-your-own-device (BYOD) policies.
Each of these protocols comes with its own strengths and ideal use cases. VPN concentrators are typically equipped to support several protocol options at once, ensuring compatibility across a variety of client devices and security requirements.
What is the difference between a VPN concentrator and IPsec encryption?
It’s easy to get the roles of a VPN concentrator and IPsec encryption mixed up, but they serve distinct (yet complementary) purposes within a secure network. Think of a VPN concentrator as the architect and traffic controller—it is the dedicated hardware or virtual appliance responsible for creating, maintaining, and managing multiple VPN connections, often for businesses with lots of remote users. This device keeps everything organized, handles user authentication, and ensures encrypted tunnels are up and running 24/7, even when hundreds of users try to connect from across the globe.
IPsec, on the other hand, is not a device at all—it’s a protocol suite. If the concentrator is the architect, IPsec is the sturdy material used to build the walls and roof. It provides the actual encryption and security for your network traffic by scrambling data into unreadable packets and then decrypting them once they safely reach their destination. In most cases, a VPN concentrator will use protocols like IPsec to power its secure tunnels, but IPsec can also be used independently with other devices, such as firewalls or client-based VPN software, like what you might use with OpenVPN or certain enterprise solutions.
In summary:
- VPN concentrator = The device that manages and orchestrates many secure connections.
- IPsec = The method of encrypting and protecting data as it travels through those connections.
Understanding this distinction helps clarify how complex networks remain both accessible and secure—even when employees log in from a café halfway around the world.
What is a VPN Router?
A VPN router is a WiFi router with VPN client software installed on it. The router encrypts all of the traffic sent or received over your WiFi network.
With a standard WiFi router, you need to install the VPN app on every device before you can use it to connect to your VPN network. Whereas a VPN router has VPN client software already installed on it and you can connect all your devices to the VPN network without installing VPN software on each device. The router provides privacy and security for all your devices without any hassle. VPN router is meant to be used in home networks or small networks with few users.
Difference between VPN Concentrator and VPN Router
Though both VPN Concentrator and VPN router operate in the same way they also differ in several other ways.
A VPN provides secure remote access for individuals, typically connecting a single user securely to a remote network. However, a VPN concentrator manages and maintains secure connections for multiple enterprise users at once, offering scalability and centralized control for large-scale deployments. The Concentrator can handle thousands of users at the same time and create a VPN tunnel for each of them making it ideal for corporate environments where the employees can safely connect to their company network remotely from anywhere in the world.
Whereas, a VPN router has certain limitations to the number of people it can handle. A VPN router is meant to be used for small businesses where only a few users have access to the private network. VPN Concentrator may be described as an improved VPN router, which is more suited for large businesses rather than a home network or small businesses.
Additional Advantages of VPN Concentrators
Apart from supporting more users, VPN concentrators have other advantages over VPN routers. The modern Concentrator VPN has a highly effective firewall, uses advanced encryption techniques, provides data encryption, allows the creation of VPN tunnels, authenticates multiple users, and also assigns tunnels for each of the connected users.
Seamless User Experience and Centralized Control
One of the key benefits of a VPN concentrator is its ability to integrate seamlessly with VPN client software. Once initiated, users are automatically connected through secure tunnels without needing to manually configure each session. This makes remote access both simple and secure for employees.
A VPN concentrator also centralizes network management, giving administrators full control over VPN connections and security policies. Fine-grained access controls can be implemented, allowing network admins to restrict user access to sensitive areas based on roles or attributes.
Advanced Routing and Scalability
As a more advanced piece of network equipment, the concentrator manages complex protocols and routing algorithms that go beyond the capabilities of standard routers. It can efficiently handle high volumes of secure connections, making it highly scalable for organizations with many remote users. This means that as your business grows, the VPN concentrator can quickly accommodate additional employees without increasing latency or setup complexity.
In summary, while a VPN router is suitable for small-scale use, the VPN concentrator is built for enterprises that require robust security, centralized management, and the ability to support a large, distributed workforce.
Disadvantages or Limitations of a VPN Concentrator
While VPN concentrators offer robust functionality for businesses with large remote workforces, they are not without their drawbacks. It’s important to weigh these considerations before deciding if a VPN concentrator is right for your organization.
1. High Upfront Investment
Deploying a VPN concentrator tends to involve substantial upfront costs. The hardware itself is generally enterprise-grade, and setting up the necessary infrastructure requires a meaningful financial commitment—a factor that may put off small to mid-sized businesses. Prices can vary significantly depending on the manufacturer, performance specs, and capacity of the device. For instance, a basic VPN concentrator that supports only a few dozen connections might start around $200, while more advanced models capable of handling hundreds or even thousands of secure tunnels can easily exceed $1,000. As your organization’s needs grow, so too does the investment, making it crucial to carefully consider both current and future scalability requirements before making the leap.
2. Bandwidth Constraints
Even though concentrators are designed to handle a large number of connections, they do have limits. If too many users log in at once, the available bandwidth can be stretched thin, resulting in slower speeds or reduced performance for everyone connected.
It’s also worth noting that, like any VPN solution, concentrators route all internet traffic through encrypted tunnels. This additional step naturally introduces some latency, as requests must be processed and secured before reaching their destination. The result? Web pages may take a bit longer to load, and in rare cases, requests might even time out or drop entirely during periods of heavy use. For most organizations, the trade-off is a connection that’s only slightly slower than direct access—often a small price to pay for the added security and privacy a VPN concentrator provides.
3. Complex Setup and Management
Unlike plug-and-play solutions, VPN concentrators usually demand more technical expertise. Installation, integration, and ongoing maintenance require network professionals who are familiar with secure configurations—making it less practical for organizations without dedicated IT staff.
4. Performance Limits and Scaling Issues
There’s a ceiling to how much traffic a single device can handle. If your needs outgrow the hardware, you’ll need to invest in additional concentrators, which increases both complexity and expense. Unlike cloud-based VPN solutions from providers like NordVPN Teams or Perimeter 81, scaling with hardware can be cumbersome.
5. Single Point of Failure
Because all user connections typically run through the concentrator, any hardware failure can bring remote access for the entire organization to a halt. This creates a risk for large organizations where continuous uptime is essential.
While these limitations don’t outweigh the significant benefits for many large enterprises, it’s wise to consider them carefully—and explore whether a more scalable or simpler VPN solution might serve your network’s needs more efficiently.
Alternatives to VPN Concentrators
If the scale, complexity, or price point of a VPN concentrator feels like overkill for your environment, you’re in good company. Not every organization needs a heavy-duty solution to give their users a secure remote connection. Let’s look at some of the most popular alternatives that may be a better fit for smaller businesses or distributed teams.
VPN Clients:
For individuals and smaller teams, VPN client software is the go-to option. This type of software is installed on each user’s device and connects directly to a VPN server, encrypting traffic and providing secure access to resources. VPN clients are generally straightforward to set up—just download, configure, and connect—but keep in mind they don’t scale as smoothly as concentrators. If you’re responsible for more than a handful of users, managing and troubleshooting each client can get tedious fast.
VPN Routers:
If you need to secure all traffic from a specific location or office, a VPN router is worth considering. These devices encrypt the internet activity of all devices on your local network—without the need for users to install additional software. VPN routers are excellent for protecting at-home offices or smaller branch locations, but they don’t help users who are constantly on the move or working from different sites. For globetrotters and road warriors, pairing this solution with device-specific VPN apps can close the gap.
Site-to-Site VPNs:
Organizations with multiple physical locations—think: regional branches or partner offices—often use site-to-site VPNs to create encrypted tunnels between separate networks. This setup is managed at the network level, typically involving a bit of configuration on both ends, but it allows entire offices to connect securely over the internet. Site-to-site VPNs can be a solid alternative to concentrators, as they link locations rather than just individual users.
Cloud-Based VPN Solutions:
Lastly, cloud-based VPN services, such as those offered by NordLayer or Perimeter 81, provide scalable, managed alternatives that don’t require specialized hardware. These options offer web dashboards for centralized control, flexible licensing, and can be deployed in minutes rather than hours or days. They’re built to accommodate growth and can sidestep many of the scaling headaches that come with physical appliances.
When considering alternatives, it’s critical to assess your organization’s size, remote work requirements, and IT capabilities. The right solution should strike a balance between security, scalability, and ease of management—without bogging your team down with unnecessary hardware or technical hurdles.
Other Secure Remote Access Solutions
Of course, traditional VPNs aren’t the only game in town when it comes to protecting remote connections. If you’re aiming to enhance security or minimize hassle, several modern technologies offer remote access without relying solely on VPN infrastructure.
- Zero Trust Network Access (ZTNA):
ZTNA solutions take a fundamentally different approach to security. Rather than granting broad network access, they verify each connection and user, assigning permissions only to the specific apps or resources needed. This “never trust, always verify” model limits your risk surface, especially when users are working from everywhere. - Remote Desktop Gateways:
For organizations with remote desktop or Windows environments, gateway servers can route secure connections directly to internal machines. These often use protocols like RDP over HTTPS, adding an extra encryption layer while locking access down to specific endpoints. - Software-Defined Perimeter (SDP):
SDPs create dynamic, invisible perimeters around cloud or on-premises resources. Users must authenticate before any network visibility or access is granted—which means attackers can’t see, let alone target, protected servers or databases. - Multi-factor Authentication (MFA) with Secure Web Gateways:
Sometimes, simply strengthening login procedures—like requiring MFA in combination with secure web gateways—can provide a lightweight yet powerful defense for cloud app access, especially for organizations fully in the cloud.
Each of these options brings unique strengths and potential trade-offs, so the best fit will depend on your specific remote access needs, regulatory requirements, and the resources you want to protect. Often, a layered approach—mixing elements from a few of these solutions—delivers the best of both worlds: security and practicality.
Notable VPN Concentrator Manufacturers
If you’re considering integrating a VPN concentrator into your network infrastructure, knowing which manufacturers lead the market can help guide your research.
Several well-established networking companies produce reliable VPN concentrators designed to support enterprise-level demands:
- Cisco: Renowned for its robust enterprise networking solutions, Cisco’s VPN concentrators are favored for their scalability, security features, and ease of integration—making them a frequent choice for organizations with large workforces.
- Aruba Networks: A subsidiary of Hewlett Packard Enterprise, Aruba Networks offers versatile hardware that can be configured as VPN concentrators, particularly well-suited for businesses prioritizing mobility and secure remote access.
- Mitel (formerly ShoreTel): Known for their expertise in telecom infrastructure, Mitel supports secure VPN connectivity for organizations needing seamless, encrypted voice and data communications across distributed locations.
When evaluating options, consider factors like compatibility with your existing network, ease of management, and the scalability to grow alongside your business. Choosing a trusted provider ensures both reliable performance and comprehensive support as your remote access needs evolve.
Difference between a VPN Concentrator and a VPN Client
While we’ve already touched on the distinction between a VPN concentrator and a VPN router, it’s equally important to clarify how a VPN concentrator differs from a VPN client.
A VPN concentrator is designed as a centralized device to manage and secure connections for a large number of users all at once. Think of it as the central gatekeeper for an organization’s remote workforce—it builds, assigns, and secures multiple VPN tunnels, making it a perfect fit for enterprise environments where hundreds or even thousands of employees need remote access at the same time.
On the other hand, a VPN client is simply the software you install on individual devices, like your laptop or smartphone. The VPN client’s job is straightforward: it creates a secure tunnel from your device to the company’s network, most often connecting back to a VPN concentrator or a VPN server somewhere at headquarters. This allows a single employee to work remotely, sending and receiving encrypted data as if they were plugged in at the office.
In summary:
- VPN Concentrator: Centralized device managing secure tunnels for many users, primarily used by large organizations.
- VPN Client: Software installed on each user’s device, providing individual secure connections, suitable for single users connecting to the network.
This division of roles ensures that whether you’re managing a global team or logging in from a coffee shop, your sensitive business data is kept safe and sound.
How does a VPN Concentrator compare to a Site-to-Site VPN?
A VPN Concentrator is tailored for businesses that need to support a large number of remote users, such as employees traveling or working from home. The concentrator excels at creating secure individual tunnels for each user, handling connections on a per-person basis even if everyone is scattered across the globe and using a range of devices, from laptops to smartphones.
In contrast, a site-to-site VPN is designed to connect entire networks together—think of two branch offices in different cities working as if they are physically wired together. Instead of focusing on individual user access, a site-to-site VPN establishes a fixed, encrypted link between two or more locations. This allows everyone and every device at each site to communicate freely, just as they would on a single local network.
To sum up:
- VPN Concentrator: Best for managing secure remote access for many individual users, ideal for large organizations with a mobile or distributed workforce.
- Site-to-Site VPN: Best for linking two or more office locations, so entire local networks can seamlessly share resources and data.
Both approaches use encryption and tunneling, but the choice depends on whether you’re connecting people individually or linking whole offices together.
What is a VPN tunnel?
The VPN Concentrator creates a virtual private network by establishing a secure connection called a tunnel, across the Internet that users see as a private connection. The device transmits or receives plain data packets in an encapsulating form through the above VPN tunnels for delivery to their final destination. The main functions of this networking device are,
1. Establishes VPN tunnels for multiple remote users;
2. Authenticates multiple end-users;
3. Assign tunnels to the connected users;
4. Encrypts connection for secure data transfer;
5. Manages Security key;
6. Manages data transfer across the tunnel to ensure data delivery;
When do you need a VPN concentrator?
Here is an example of when you may need this networking device.
Suppose you have a business where you have employed people online from various parts of the world. There may be occasions when your people may need to access their work files as if they are physically present in your office. This is when a VPN concentrator comes in. The Concentrator VPN establishes a secure connection across the Internet to enable your workers to connect to your company’s network remotely from different points and get access to their desired work files in the office.
With the rise of digital technology—and especially after the shift to remote work prompted by COVID-19—millions now log in from home offices, cafés, or co-working spaces scattered across the globe. As working from home has become the norm for so many, the need for secure, reliable connections has never been greater. In fact, between 2019 and 2021, the number of remote workers in the United States alone tripled, surging from about 9 million to over 27 million.
This massive increase in remote access has made cybersecurity a top priority for businesses. VPN concentrators have stepped up as a crucial solution, allowing organizations to manage a large, distributed workforce. By enabling people from different cities or even different countries to connect safely to a central network, VPN concentrators provide the privacy and security needed to protect both company data and employee activities online. In essence, a VPN concentrator acts as a digital gatekeeper—making sure remote connections stay private, encrypted, and out of the reach of cyber threats.
Do I need a VPN concentrator for my organization?
If your organization has a significant number of employees who regularly connect remotely—whether from home, client sites, or across international borders—a VPN concentrator can be an essential tool. It streamlines the process of managing numerous secure connections, making it far easier to oversee security for a distributed workforce.
Consider a VPN concentrator if:
- You need to connect dozens or hundreds of remote workers at once.
- Employees frequently require access to internal resources from locations outside the office.
- Your business can’t afford to compromise on data privacy and security.
- You want to simplify network management rather than juggling individual VPN connections for each user.
Small businesses with just a handful of remote users may find a basic VPN setup sufficient. But as your team grows—or if you need to connect multiple offices—a VPN concentrator, like those offered by Cisco and Fortinet, becomes invaluable for scalability, reliability, and centralized control. It’s a practical investment that keeps your network agile without sacrificing security.
Frequently asked questions
Now that I have explained in detail what is VPN Concentrator and how it works let me also address some of the related questions often asked by the people.
What is a VPN tunnel?
A VPN tunnel is an encrypted connection across the Internet between the user’s device and the home or company’s private network. The users see it as a private connection.
How do I set up a VPN in Windows 10?
Follow the steps below to setup VPN in Windows 10:
>Click on the Windows button;
>Go to Settings > Network & Internet > VPN;
>Click on Add a VPN connection;
>Select Windows for your VPN provider (built-in);
>Give your VPN a name under Connection;
Does a VPN slow down your internet?
Yes, using a VPN does slow down your internet speed. It depends on a few factors such as the distance of the server to which you are connected, the level of encryption of traffic, server load, and the internet speed.
You may also like to read: How to get free internet on Android using built-in VPN client
Conclusion
To sum up, if you are running a small business where there are not too many users to access your private network or if you want to set up a small VPN to allow users to access your home network remotely, a VPN router would perhaps be a good option for you.
On the other hand, if you need a larger solution for your business that needs to handle considerable loads requiring a much higher number of people to connect to your company network at the same time, a VPN Concentrator would be the way to go.
As already explained in the post under ‘What is a VPN Concentrator’, Concentrator VPN is used by large businesses that operate multiple systems that are connected using a network.